Virus Detection & Device Isolation
SCENARIO: Malicious Payload Detection
ENVIRONMENT: Controlled Lab (Windows 10 VM)
A technical demonstration of incident response procedures utilizing Microsoft Defender for Endpoint to halt lateral movement by completely isolating a compromised host off the network while pulling forensic telemetry.
Operational Response Lifecycle
The standard incident response checklist adhered to upon confirming malicious file execution.
1. Detect
Identify Antivirus events universally using Kusto.
2. Isolate
Sever host access to LAN/WAN to prevent spread.
3. Collect
Acquire forensic packages directly via MDE agent.
4. Release
Restore standard network bridging post-remediation.
Query & Detection
Initiating the response playbook requires solidifying the scope of the virus alert. We executed an advanced hunting query to directly poll DeviceEvents specifically for internal Windows Defender AV alarms.
DeviceEvents
| where ActionType == "AntivirusDetection"
| project Timestamp, DeviceId, DeviceName, FileName, FolderPath
| sort by Timestamp desc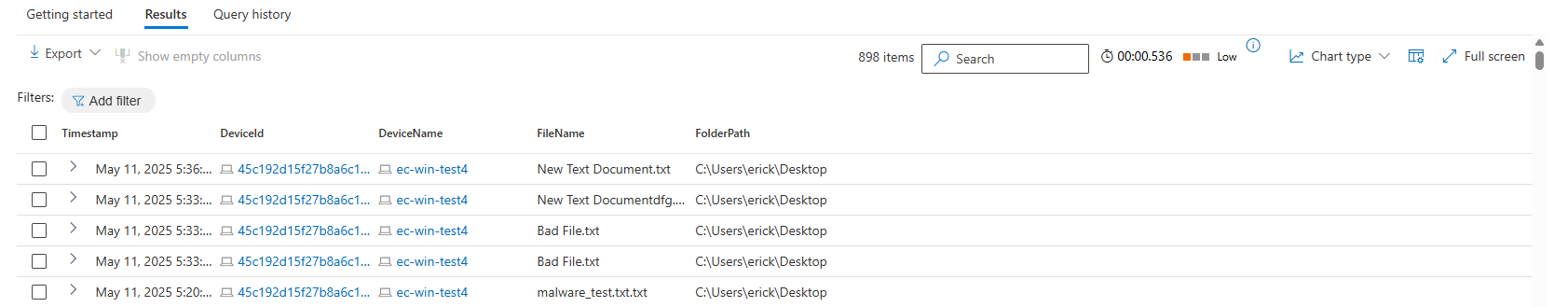
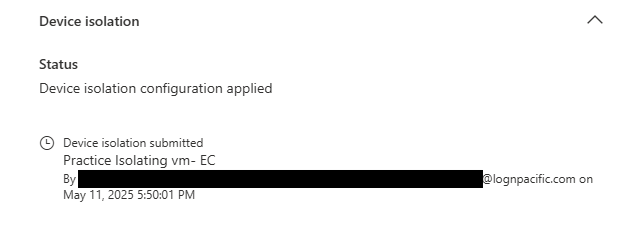
Enforce Isolation
With malicious activity confirmed, immediate containment is critical. Isolation severs the host's ability to speak to the internet, domain controllers, and local subnets—restricting communications solely to the Microsoft Defender sensor heartbeat.
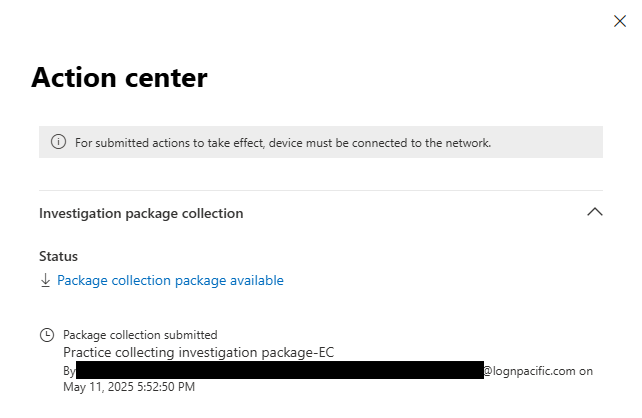
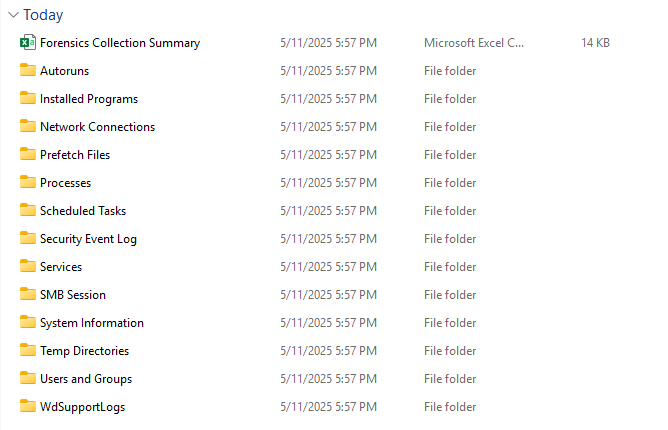
Forensic Package Acquisition
While the host is isolated, we utilize MDE's remote response capabilities to pull a full Investigation Package. This zip archive contains crucial volatile data including Autorun keys, Active Network Connections, Process trees, and Security Event Logs over the last 30 days.
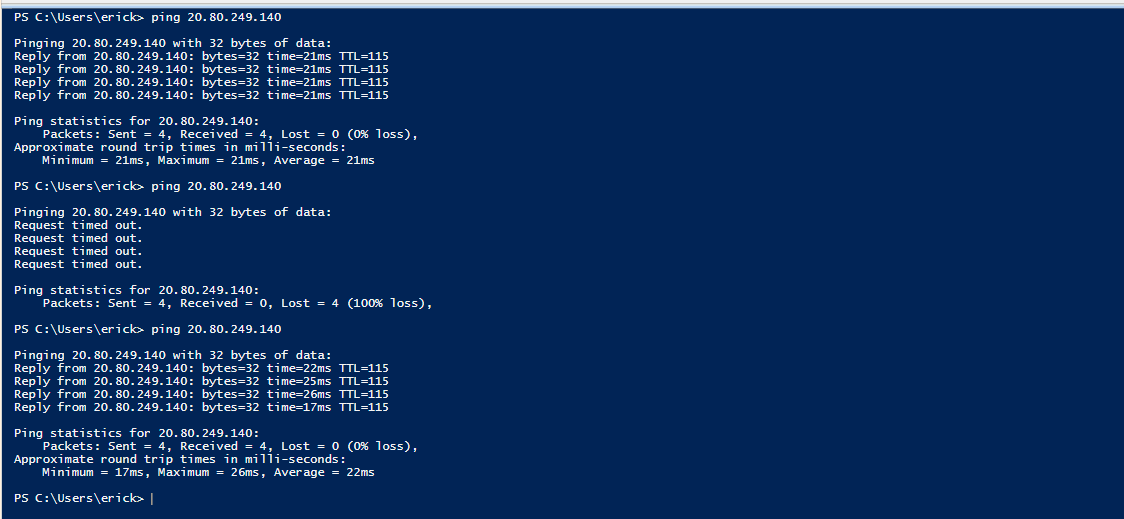
Network Verification
Host was actively able to resolve and reach external WAN infrastructure (8.8.8.8).
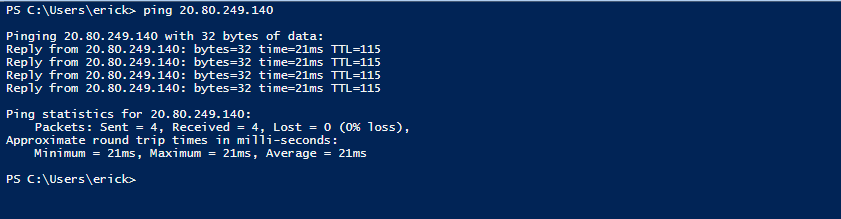
Host traffic was entirely dropped natively by the Windows filtering platform (Transmit failed).

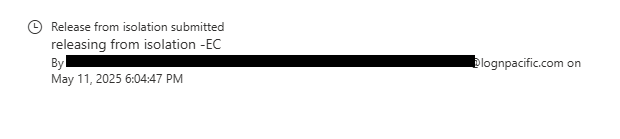
Remediation & Release
Following the extraction of evidence and subsequent deletion of the offending malicious artifacts via Live Response shell, the machine was declared clean. A release command was dispatched, seamlessly reconnecting the VM back to the corporate LAN and internet instantly.